This event will stress the importance of cybersecurity and offer unique challenges and opportunities to the San Diego Community. The City of SD recognizes the potential this occasion could bring to the city and has provided financial support to take this event to the next level.
Code with us for Hack-o-ween
Join us for Hack-o-ween, a VR/AR Hackathon produced by the AT&T Developer Program and CyberTECH. Hackathons are coding competitions, where individuals and teams build apps and games from scratch over a specified time period. The apps are then pitched to judges and prizes award for the best apps. Hackathons are a great opportunity to learn new technologies, network with fellow developers, enjoy some food, most importantly have some fun!
The Hackathon will be held in downtown San Diego at CyberTECH’s cybersecurity incubator and shared workspace, CyberHive, starting the evening of Friday, Oct 27 and ending the evening of Sunday Oct 29. See the full schedule below.
It’s Hack-o-ween!
Code in costume if you want! Bring your favorite cosplay, neopixel wearable, or that SpongeBob outfit. Street clothes are fine also!
Schedule
The following is a list of the weekend’s agenda:
Day 1 – Friday
6PM – Dinner is served and networking
7PM – Event kickoff
8PM – Pitch ideas, form teams, and start coding!
9PM – Equipment loaning
12AM – Venue closes for the night; you may continue working on your project offsite.
Day 2 – Saturday
9AM – The fun continues with breakfast served in the morning! Work with the teams from Day 1 to complete the app.
1PM – Lunch is served
4PM – TEAM REGISTRATION DEADLINE
7PM – Dinner is served
CyberTECH will be open OVERNIGHT on Saturday! Thank you to CyberTech for keeping the hackathon non-stop!
Day 3 – Sunday
9AM – Breakfast served
1PM – CODE FREEZE. First round of judging. Lunch is served
4PM – Top teams present and winners announced
Prizes
The following prizes will be awarded after the fast pitches are completed and the judges have convened:
Best Hackathon Overall App
$1000 in Amazon gift cards for the team
Membership to CyberTech ($1680 value)
Best Smart City Hack
$500 in Amazon gift cards for the team
3 month hot desk at CyberTech ($750 value)
Best VR/AR Hack
$500 in Amazon gift cards for the team
3 month hot desk at CyberTech ($750 value)
Judging Criteria
Apps will be judged based on the criteria below and weighted accordingly.
33% Weight – Ability to clearly articulate what your app does
33% Weight – Originality of idea
33% Weight – Creative use of technologies discussed at the event
TO REGISTER CLICK HERE
Hackathon Legal
Hackathon terms: http://bit.ly/2fb1fdH
We expect all participants to abide by the Hack Code of Conduct: http://hackcodeofconduct.org/attdeveloper
Social Media
Follow us @attdeveloper and @CyberHiveSD for live updates and photos from the event
Use #atthack in your tweets
Like us on Facebook https://www.facebook.com/ATTDeveloper
Speakers
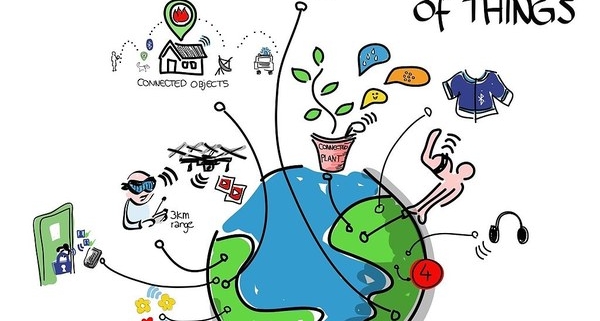
Darin Andersen is a distinguished Internet of Things (IoT) and cybersecurity professional with over 15 years of experience in the security industry. In 2013, Mr. Andersen founded CyberTECH (CyberHive and iHive Incubators), a global cybersecurity and IoT network ecosystem providing cybersecurity and IoT resources, strategic programs and quality thought leader IoT Forums across the nation. Darin is also founder of CyberUnited, a cybersecurity, big data and predictive analytics firm that applies a behavioral psychology framework via machine learning, data, analytics and inferential algorithms to determine and prevent identity and insider threats within the enterprise, academic and government organizations.
Sponsors